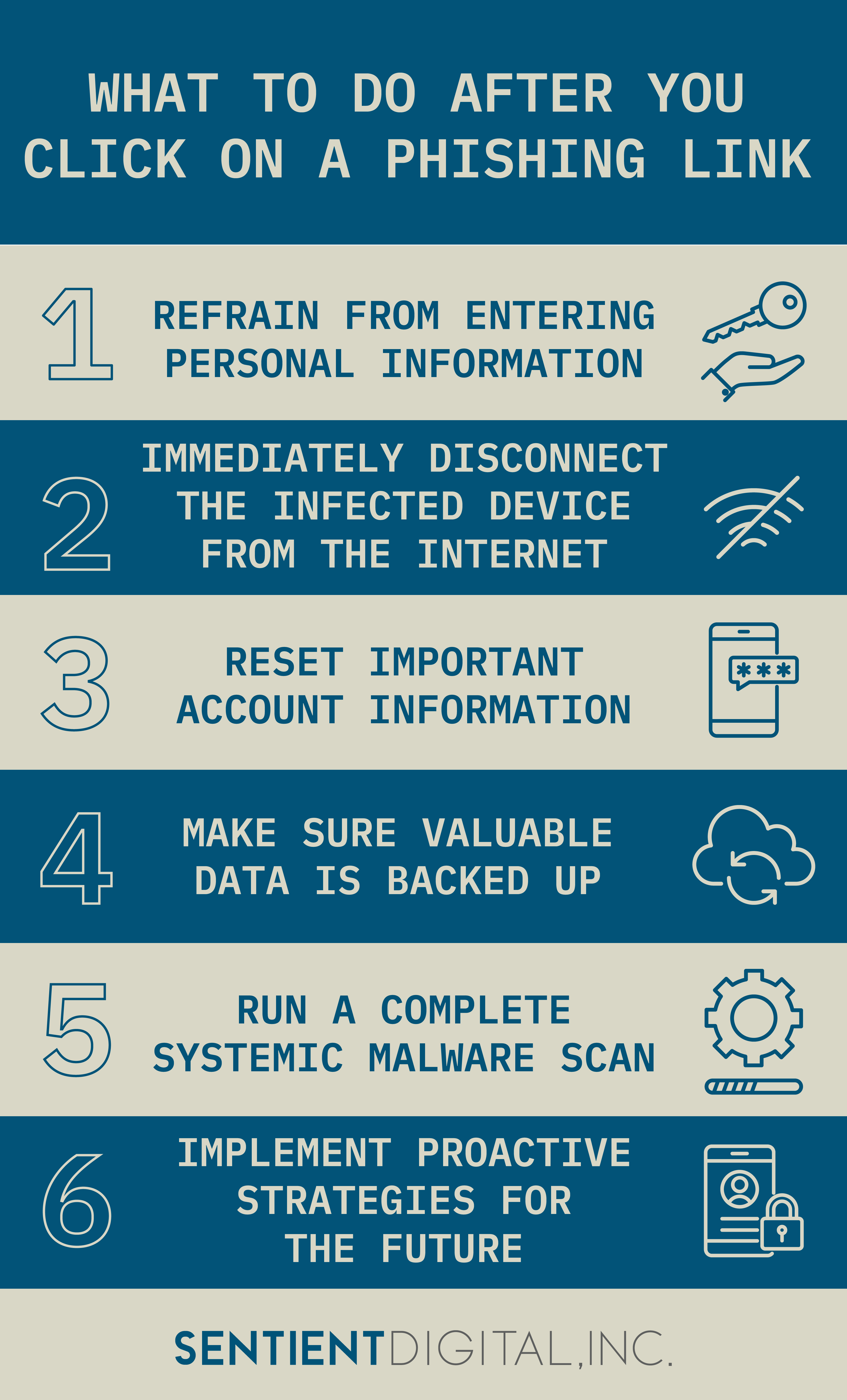
Phishing links deployed through fraudulent email addresses have become increasingly sophisticated, and even the most proactive, secure environments need to be prepared with emergency reactive protocols. In addition to alerting your IT or security team, here’s what to do after you click on a phishing link:
- Refrain from entering personal information
- Immediately disconnect the infected device from the Internet
- Reset important account information
- Make sure valuable data is backed up
- Run a complete systemic malware scan
- Implement proactive strategies for the future
Continue reading to prepare yourself—and your organization—in the event of a future phishing scenario.
What Is a Phishing Attack?
Phishing attacks are one of the most common tactics deployed by hackers in efforts to gain access to valuable data, targeting millions of individuals every day.
In essence, phishing occurs when fraudulent agents pretend to be legitimate entities or officials soliciting private credentials or information through live HTTPs, downloads, or attachments deployed mainly through emails. After you click on a phishing link or malicious attachment, it will automatically install malware or ransomware, or else redirect you to a conversion page that requests the input of your personal information.
Phishing scams target both individuals and organizations of all sizes, often using susceptible individuals as conduits to access larger corporate databases. Phishing that targets sensitive company data may be seeking protected intellectual property, client databases, company funds, and more. Most phishing scams are after personal identifying information (PII), which includes bank account or credit card information, social security numbers (SSNs), login credentials, and account numbers, among others.
The Consequences of Phishing Attacks
Phishing attacks have continued to play a major role in cybercrime and have increased in sophistication since their inception in the mid-1990s. 2020 witnessed an unprecedented rise in cybercrime across the board, with phishing attacks accounting for 22% of all recorded data breaches. Because of the recent spike in remote work due to the ongoing pandemic, phishing scams have become increasingly commonplace while employees must rely on digital communications to authenticate interpersonal requests and solicitations.
Such phishing attacks are incredibly costly. Research shows that the average company with 10,000 employees spends about $3.7 million per year on phishing attacks and the ensuing disaster recovery processes and productivity losses that follow. Besides front-end revenue loss, the other effects of phishing attacks include major declines in stakeholder, user, and customer trust, leading to long-term organizational frailty.
Knowing exactly what to do after you click on a phishing link can dramatically reduce the potential consequences.
What to Do After You Click on a Phishing Link
The moments following a click on a phishing link are critical. If you have an IT department or security team, be sure to alert them to the incident first and work with them to mitigate the situation.
Here are 6 immediate steps that detail exactly what to do after you click on a phishing link.
1. Refrain from Entering Personal Information
Ideally, you are able to identify a phishing attempt before you input any sensitive account information. If you do share any sensitive information, such as a bank account number, you should contact your bank or other relevant institutions immediately.
But even if you refuse to enter your information after you click on a phishing link, there is still the possibility of discreet malware installation. Be sure to follow the next steps to help protect yourself.
2. Immediately Disconnect the Infected Device from the Internet
Like biological germs, certain malware infections can easily spread through network attacks. By disconnecting the infected device from the Internet, you can help protect your network and other connected devices from the threat.
Isolate the infected device from the network by unplugging it from any wired connection and turning off wireless Wi-Fi capabilities completely.
3. Reset Important Account Information
Any account information entered after you click on a phishing link is by definition compromised. Reset the credentials for the affected account as well as any secondary accounts that the first may be linked to.
Use industry-standard guidelines for generating strong passwords and make sure each account has its own unique password. In addition, it’s a good idea to implement multifactor authentication protocols for added security.
4. Make Sure Valuable Data Is Backed Up
Once your device is securely offline, you’ll want to ensure that high-priority files are protected from being damaged, compromised, ransomed, or lost as the attack progresses. The recovery process may also involve data loss, as it removes malware from any affected operating systems.
Use an external device such as a USB, hard drive, or OTG drive to transfer data to a secure and controlled location. But before you connect this device anywhere else, have your IT department or security professionals take a look to make sure it’s not compromised by the phishing attack.
5. Run a Complete Systemic Malware Scan
Because contemporary malware is increasingly hard to detect and outwardly presents as legitimate, it may be wise to invest company resources into hiring trained cybersecurity experts to conduct vulnerability remediation scans.
Front-end security costs are negligible compared to the expenses of lost revenue and press fallout down the line after a cyberattack. Effective malware scans save time and valuable resources when performed quickly and thoroughly.
6. Implement Proactive Strategies for the Future
Knowing what to do after you click on a phishing link in the short term is crucial. But planning for the future is just as important. After an attack, be sure to review your security protocols and make sure you’re well-protected.
Phishing attacks have been around for nearly three decades, and they will continue to pose threats to the digital environment for years to come. Coming face to face with a threat like this can be an important catalyst for initiating a company-wide cybersecurity transformation.
A proactive cybersecurity strategy may involve an intersectional combination of staff training, threat hunting, cyber monitoring, and network fortification. Keep reading for an overview of the different types of phishing attacks you may face, as well as different strategies that can help protect your organization against future attacks.
Types of Phishing Attacks

Basic email phishing has gradually matured as a threat, and specialized types of phishing have evolved over time. Familiarizing yourself with more specific phishing tactics will help you recognize them in the future.
- Spear Phishing: Spear phishing occurs when fraudulent emails are customized to include a target’s personal information, thereby making the ruse more convincing. Hackers may sample and collect data from a variety of third-party platforms—Instagram, LinkedIn, and Facebook, for example—in order to list a target’s name, company, position, and work phone number so that they are more likely to hand over their data.
- Angler Phishing: Angler phishing involves hackers combing and vetting social media posts for upset customers. The cybercriminal will reach out to these customers, disguised as a representative from the offending company’s customer service department. This faux support leads vulnerable individuals to click “help” links that install malware on their computers.
- Whaling: Whaling operates on many of the same principles as spear phishing, except this tactic is specifically targeted at high-ranking CEOs and other executives. These urgent and personalized solicitations usually encourage an immediate transfer of funds or access to protected corporate networks.
- Vishing: Unlike the aforementioned techniques, vishing scammers impersonate entities over the phone instead of via email. They may use Voice over Internet Protocol (VoIP) to convince individuals of their legitimacy or draw on personal data gleaned from social networks to appease skeptical targets.
- Smishing: Smishing is similar to vishing except that cybercriminals use SMS texting to deploy their attacks. The limitations of smartphone security systems means that there are relatively few preventative measures in place to weed out smishing campaigns. Smartphone users who are checking texts on the go may be particularly distracted and, therefore, susceptible.
Proactive Strategies Against Phishing Attacks
Phishing attacks can happen to anyone, regardless of their digital proficiencies. Previous attacks, though highly unfortunate, better prepare us to adopt preventative stances in the future.
Today, we have more holistic access to proactive defense tactics than ever before. Here are several strategies to better identify and prevent phishing attacks.
Awareness Campaigns
In 2020, it was reported that 97% of targeted users were unable to identify a phishing attack. Knowing what to do after you click on a phishing link is only helpful if you’re able to recognize the attack in the first place. Though this statistic seems formidable, the problem can be easily remedied through the widespread implementation of educational and awareness programs.
It is crucial to teach employees how to avoid falling prey to phishing scams by identifying them early on. The most formidable weapons against phishing are preparedness and awareness.
If users can easily identify suspicious links, then there is little threat they will click on a phishing link. In-house educational campaigns in the form of training sessions, handbooks, and webinars are cost-effective methods to raise awareness and avoid trouble in the first place.
Embedded Reporting Systems
Whether they’ve actually clicked on a phishing link or not, clear and concise reporting systems direct the affected employees up a vertical chain of command so that security protocols can be immediately enacted by upper management. Users should also report phishing emails as spam from their email accounts.
Verification Protocols
In order to convince their targets to surrender personal data, click bogus links, or download malicious attachments, phishing attackers may impersonate trusted sources, such as:
- Upper management, business owners, or CEOs
- Customers or clients
- Partners or stakeholders
- Contracted suppliers
- Customer service representatives
- Friends, coworkers, or family members
By learning to separate impersonators from authentic requests, users can easily avoid falling victim to all varieties of phishing.
- Check source emails—not just sender names—for misspellings. Avoid those sent from public domains altogether.
- Be wary of emails or texts with bad grammar, suspicious links, or a sense of urgency to act.
- Check any company phone numbers included in an email. Make sure they are listed on the company’s official website before calling.
Stay Protected from Phishing with Sentient Digital

Now that you understand exactly what to do after you click on a phishing link, it’s time to take the most important step: preventing it from happening in the first place. Sentient Digital provides world-class security services for defense, federal, and commercial clients.
Our professional IT services tailor security solutions to fit the unique needs of your organization. Our strategies are scalable, resilient, and intersectional, ensuring that you’ll have end-to-end protection from phishing, malware, SQL injections, and other types of malicious attacks.
Stay secure by contacting us today to get started on your personalized security plan.