Products
Anti-Submarine Warfare (ASW) Products
Ongoing Research Initiatives
This initiative pursues two branches of sonobuoy-based underwater communication technology to improve situational awareness. The first is a method of layering a sonar pulse with a gentle signature that allows for source validation and deconfliction at the receiver. The second method is a communication scheme that uses modified sonobuoys to transmit acoustic packages to unmanned underwater vehicles.
HoloGRAMS (Holistically Optimized GRAMS) substantially enhances ASW capabilities and significantly reduces operator workload. HoloGRAMS applies advanced signal processing techniques to leverage low SNR and “out of band” signatures, performs additional information processing to improve signal metadata quantification, and integrates efficient data visualization strategies to consolidate vast pools of sensor data into actionable intelligence. HoloGRAMS supports both the Navy’s need for an automated yet transparent ASW analysis tool but also commercialization opportunities in FMS and civilian markets.
GRAMS-Cloud will be a DISA approved, fully cloud-native, GRAMS-inspired ASW solution, supporting commercial/government cloud, on-premises, or workstation installations. All services are cloud-native with multi-tenancy and advanced Aspire orchestration. GRAMS-Cloud implements DevSecOps workflows and pipelines, allows for user collaboration and shared datasets, and adds robust scalability for high-volume usage and resource-intensive processing.
The Geospatial services in GRAMS-Cloud allow rapid import and 3D visualization of KML/KMZ datasets via drag-and-drop and long-term data storage. A robust collection of draw tools allows the imported layers to be annotated and marked for further analysis or mission reporting. Both the imported datasets and their additional markings can be moved to persistent cloud-based storage and instantly shared with other authorized users.
GRAMS-Edge is a containerized version of GRAMS-Cloud optimized for on-premises and workstation scenarios.
The USA Echo Repeater is a testing platform developed to support the development of next generation and experimental sonobuoys. Utilizing expertise in system prototyping, DSP, and acoustic array development, SDi has designed the water-deployable unit to serve the needs of the Navy for a configurable and real-time data acquisition and response system. The Echo Repeater operates as a self-contained and recoverable product, allowing for continuous remote operation until all sonobuoy testing has been concluded and reuse for future test efforts.
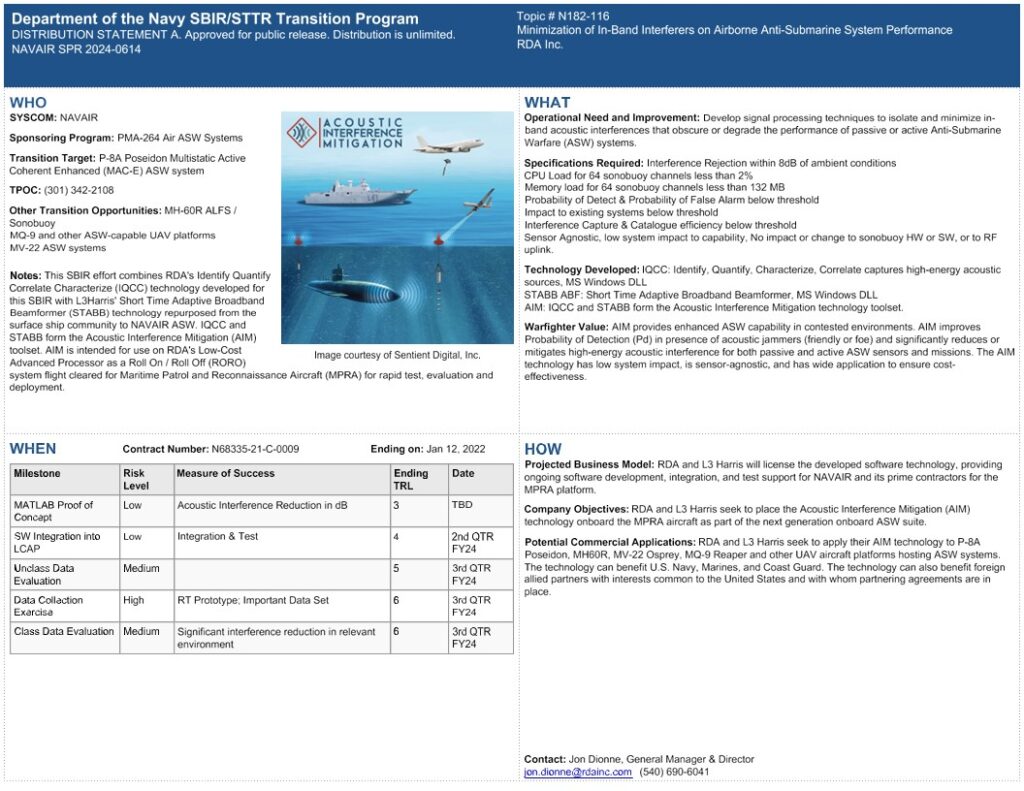
RDA’s Acoustic Interference Mitigation (AIM) provides enhanced ASW capability in contested environments. AIM improves Probability of Detection (Pd) in presence of acoustic jammers (friendly or foe) and significantly reduces or mitigates high-energy acoustic interference for both passive and active ASW sensors and missions. The AIM technology has low system impact, is sensor-agnostic, and has wide application to ensure costeffectiveness.
Navy STP Tech Talk on AIM Capability: RDA Inc’s Navy STP Tech Talk for Contract N68335-21-C-0009 (2024-25)
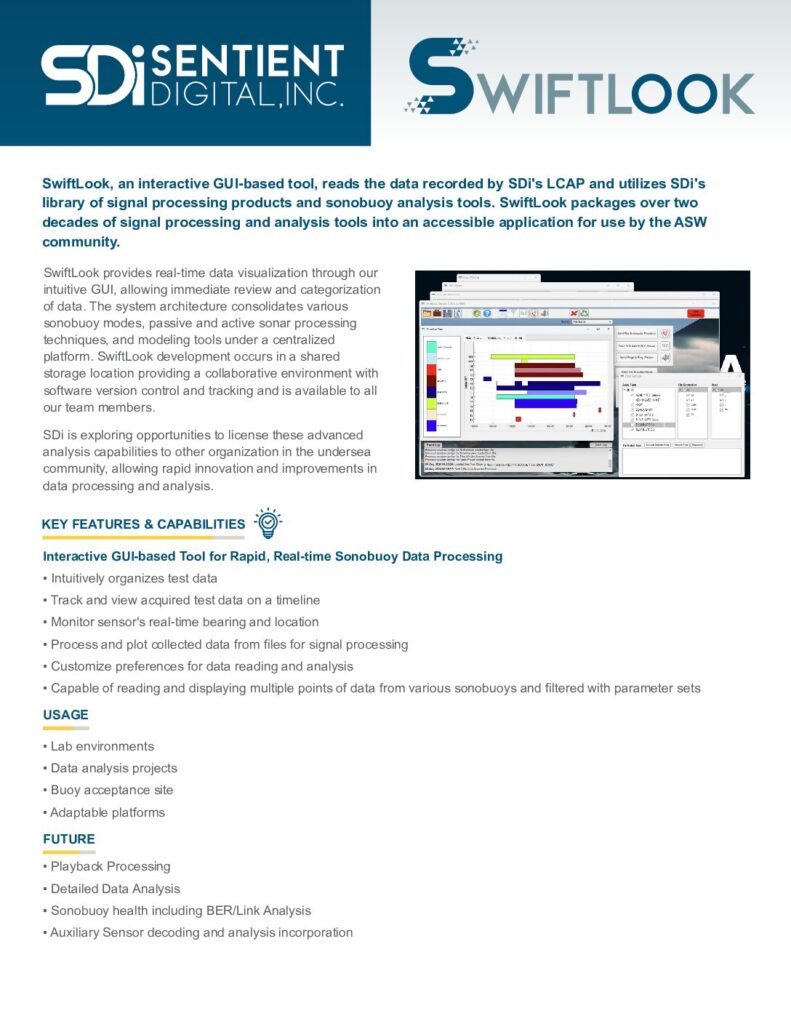
Swiftlook is a MATLAB GUI front-end to MATLAB scripts supporting LCAP analysis.